Our December 2017 update – the first in 7 months – leaps the server from 6.0.9319.281 to 6.0.9319.510. It updates 7 components on my Standard Edition Front-End.
What’s Fixed?
This update enables Location-Based Routing to support the Skype for Business mobile clients. It also fixes the following issues:
- Kb4043636 Skype for Business on Mac can’t retrieve meeting information in Skype for Business Server 2015
- Kb4043634 Sign-in dialog box is always displayed when you try to access external web services in Skype for Business Server 2015
- Kb4043638 Incorrect format of location information about an E911 call from Skype for Business on Mac
- Kb4043641 Update to add a Strict-Transport-Security header to the path of all web service responses in Skype for Business Server 2015
- Kb4043637 Update to enable Skype for Business on Mac to restrict external access in Skype for Business Server 2015
- Kb4043633 Synthetic transactions fail after installing February 2017 update for Skype for Business Server 2015
- Kb4043635 You cannot sign in Web Scheduler in Skype for Business Server 2015
- Kb4036633 “We can’t sign you in because you aren’t set up to use Skype for Business” error in Skype for Business Server 2015
- Kb4036631 Can’t join an application sharing session of meeting in Skype for Business Server 2015 that has May 2017 update applied
- Kb4036632 UCWA clients still can sign in from external networks when the external access is disabled in Skype for Business Server 2015
- Kb4036630 Can’t schedule or join a meeting after you apply May 2017 Cumulative Update for Skype for Business Server 2015
- Kb4036625 Enables the peer-to-peer file transfer feature for Skype for Business on Mac clients in Skype for Business Server 2015
- Kb4036627 Event ID 16385 floods in Skype for Business Server 2015 Director pools
- Kb4023993 LS Data MCU events 41024, 41025 and 41026 are constantly generated after you install the May 2017 .NET Framework update
- Kb4036621 Mid-call control like “Stop my video” fails if a call occurs from a VTC endpoint in Skype for Business Server 2015
- Kb4036622 “ONLINE_USER_COUNT_SETTING is immutable” error occurs if you manage chat user roles with BeginAddUsersOrGroupsToRole
- Kb4036623 “Action couldn’t be completed” error when you upload a file to a persistent chat room in Skype for Business Server 2015
- Kb4036615 Sets the default value of the “EnableDelegateManagement” attribute to “true” in Skype for Business Server 2015
- Kb4036614 “From number” is missing in the Peer-to-Peer Session Detail Report when you dial a PSTN number in Skype for Business Server 2015
- Kb4036620 Can’t join meeting by using Skype for Business Room System or Surface Hub devices in Skype for Business Server 2015
- Kb4036618 Meeting URLs are visible in search results of a search engine in Skype for Business Server 2015
- Kb4036619 Lync or Skype for Business client can’t be started to join meeting if default browser is Firefox 52 or a later version
- Kb4036612 Event Id 53530 is logged and connection to SQL database is lost in Skype for Business Server 2015 Persistent Chat Server
- Kb4036617 User move fails and many SIP messages are queued after you apply August 2016 update for Skype for Business Server 2015
What’s New?
We have a pre-req!
“To apply this update, you must have Microsoft .NET Framework 4.5.2 (Offline Installer or Web Installer) installed.”
Some new commandlets have snuck in as well:
- Get-CsAdditionalInternalDomain
- New-CsAdditionalInternalDomain
- Remove-CsAdditionalInternalDomain
- – and no, in case you think I’ve missed it, there’s no “set-“
It doesn’t appear to have made its way into the online documentation or offline help yet, so for the time being it might have to remain a mystery…
Download
Installation
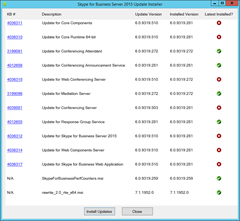
Here’s the “before” view of it going on to my Lab’s Standard Edition Front-End:
Reboot?
The installer didn’t prompt me to reboot, but I always like to give it one for good measure!
Revision History
14th December 2017: This is the initial release.
– G.




I noticed for the download that it contains a “UcmaRuntime.msp” also this time. Do you know what is it used\needed for? Most CU’s only have the .exe installer, but this one has the msp file.
-Tim
Exchange (UM) is the most obvious place, but it’s worth checking all the Trusted Apps in your topology.
Hello Greig
Hopefully you can answer my questions.
Our Skype for Business 2015 [CU4HF1] environment:
2x EDGE, 3x Frontend, 1x SQL
Do you recommend to install .Net Framework 4.6.2 or even 4.7? Because it is supported:
https://technet.microsoft.com/en-us/library/dn951388.aspx
Will CU6 fix the problem with the May 2017 .Net Framework security update?
I mean, do i still have to request new Edge Internal and
Frontend Pool Certificate with Client and Server Authentication to avoid this problem?
Article about this issue: https://goo.gl/nSwXjl
So far I only installed all .Net Framwork security updates till April 2017
Best regards,
Ihsan
CU6 does not fix the issue, tested
Hello Marars
Thank you for your response.
Ok, I will request a new edge internal and a front end pool certificate with client and server authentication.
Hi Marars,
I think CU6 only band-aids the issue. It looks like it just adds the registry key referenced in the issue’s KB as “Workaround 2”. (It may do more than that of course, but the registry key is a visible change).
– G.